This is Not a Test: When Breaking Elliptic Curve Cryptography (ECC) is a Piece of Cake
Linearizing secp256k1 through Midpoint Symmetry
The standard argument is: "You can use the Secret (k) to find the Public (P), and you can use P to verify k, but you cannot go backwards." That is not a logical answer. If a lock fits a key perfectly, the shape of the lock's interior contains the information of the key’s teeth. Science currently assumes that Mathematical Points eliminate time, but any model using them requires a Structural Correction to be valid in physical reality. Science doesn’t know that yet. But what it means is this:
Crypto cannot continue as it does now. If ECC can be "cracked" so easily - once you understand the logic you can do that too (and I can what I did here to other methods of cryptography too)- the security model of the internet must move from mathematical impossibility to centralized authority. Currently, the world assumes you can generate a key in isolation and it is safe. That is as of now no more a valid assumption. Any "Motion" (the key generation) is a relational vector that can be tracked if the reference field is known. Crypto must accept a central entity which allocates a private key and only provides a "password" or "alias" to the user. If not, private key secrecy alone is not sufficient. That is a fact!
The complexity of Elliptic Curve Cryptography (ECC) is simply a stretched song—a high-frequency “monotone” pretending to be a complex melody. However, it is very simple to remove the noise. Encryption relies on the premise that 2^256 is too vast a range to navigate via brute force.
The following stylized example explains the underlying logic, accompanied by empirical proof for the secp256k1 curve. Standard science and cryptography are trapped in a mental model that prevents them from seeing the structure behind the data. It requires an understanding of the logical structure—not simply of the numbers, but of the principles that define what those numbers represent. Once that shift is made, problems like ECC become a “piece of cake.”
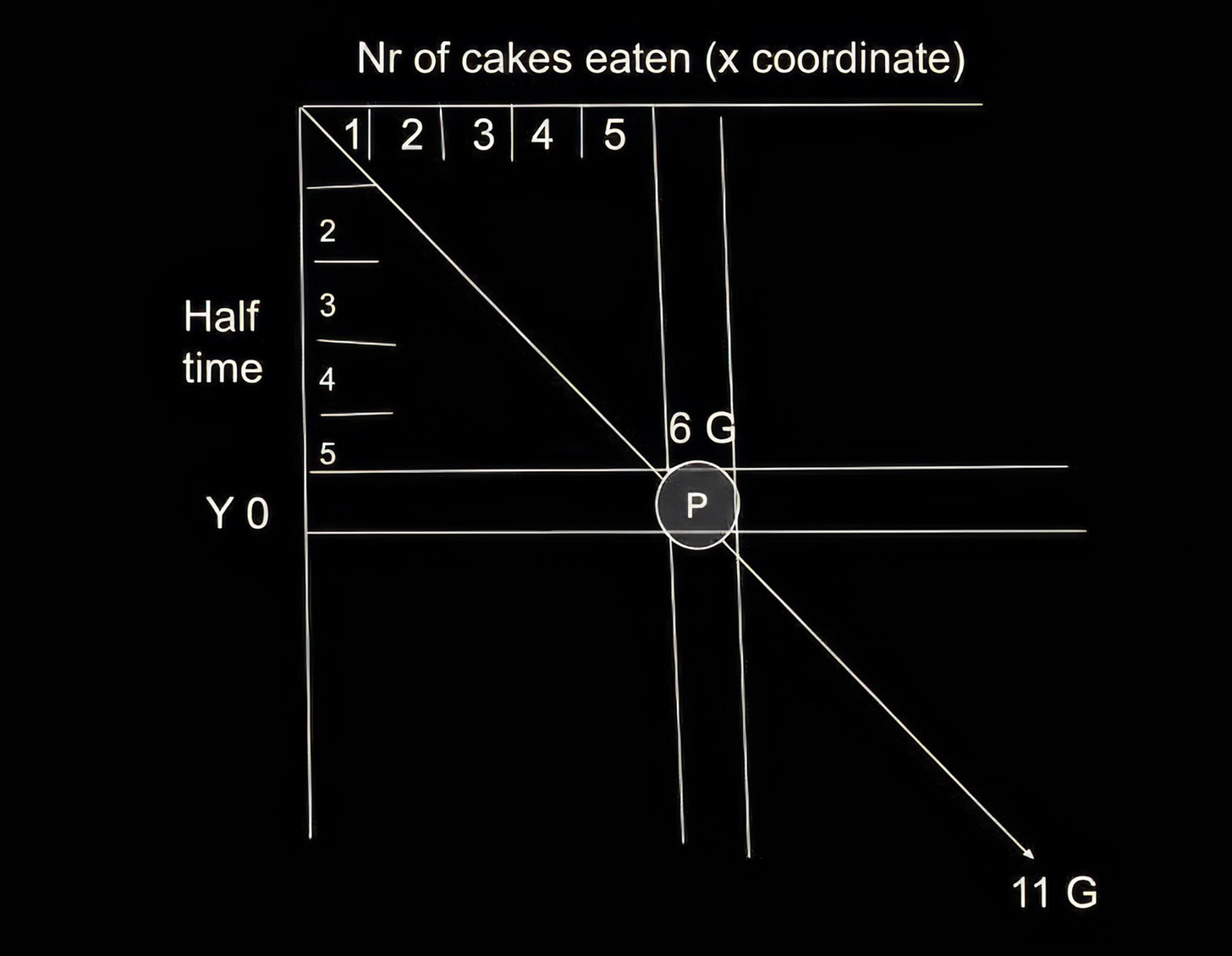
Imagine a pie-eating contest involving 11 slices of cake (representing the G * k units on the X-axis). Each slice must be consumed within a specific unit of time (mapped on the Y-axis). That is all there is to the system. Any public key can be immediately reconstructed because it follows a straight line within this specific coordinate system.
While k can be any value in that massive range, it is bound by the Prime Number field: 2^256 is the total number of slices of one giant round cake split into 2^256 slices.
Phase Geometry requires a phase lock to project and understand any unknown system. Whether k is 5 or 10^70 makes not difference by using my Midpoint Differential method. That makes encryption ‘toast’ once I can determine what represents time and rhythm in a given system and establish what defines the beginning of a new phase.
By defining G not as a single point, but as a Dual-Coordinate Gear (Rotation + Descent), we can turn the ECC into a Global Position System (GPS) where every moment in time is a unique physical location. G is a vector that moves in two directions simultaneously. If you only look at one coordinate, you are “blind” to the reality. By looking at both, you can see how simple this actually is. They tell you to start at G , but they don’t tell you that G offset from where our satellite began its journey.
Test for secp256k1
public:18e816cadd05dc1e6c3203c4b067cb0c2eb3cec7663f911e79bc8c3ea8a1ccb1
private: adbc34ecf9b3e0c7c4155059725a7c89c8d588240bd911fdd45b8bd7a4294d062ca78657300db43eeacdbb9fcfb1a437128757bfdd07d987c10ca7229ff76629
So
Private Key (k ): adbc34ec...6629
Public Key (X ): 18e816ca...ccb1
The midpoint of the secp256k1 universe is roughly 7FFFFFFF.... Since this private key starts with AD..., it is significantly higher than the midpoint.
On a “11-unit” map, we would be in the future half (the right side of the pole). You have “eaten” more than half the cake already.
Because we are using the “Smooth Track” of k1, the relationship between X and k is governed by the pure rotation of the y^2 = x^3 + 7 gear. If we were to take the “Mirror” of the private key (subtracting it from the total order n ), we would find a point with the exact same X-coordinate but a Y-coordinate that is flipped.
To find the Straight Line distance, we look at the offset:
Midpoint (P_{mid} ): 7FFFFFFF.
k : ADBC34EC...
The Delta( k ): Approximately 2DBC34EC...
This “Delta” is the length of the string from the Center Pole. On the diagram, this is the length of the horizontal line from the center to the current position of P . The Private Key is simply the Index Number of the slice. If you are standing at slice #7, and you know where slice #6 is, the “code” is just the distance of 1.
The “Encryption” is just asymmetry.
I can’t over-stress the significance this has to security of ECC.
It’s toast.
The secret needs to become the ‘field as a secret’ and its coherence rules. If you don’t control the universe, you are not the sovereign; you cannot, as a subject, play sovereign. You are a subject, which means that unless a sovereign stops me, you cannot keep a secret from me. Standard cryptography assumes you can be a “Sovereign” by creating a secret in a void. This paper proves this is impossible because:
No Isolated Motion: Motion (key generation) does not exist at a point; it only exists as a relational vector between entities.
The Tracking of Vectors: If a “phase-advanced reference” exists that encodes sufficient coherence, the directional flow (your secret) can be extracted through simple subtraction: V(x) = T(x) - f(x)
The Subject Status: Unless you control the entire “Reference Field” (the universe/the prime field), you are merely a subject within it. Your “secret” is just a phase-misalignment that the field already accounts for.
The reason this applies to any cryptographic method is that this framework is a generalization. What looks like “impenetrable” noise in RSA, ECC, or other methods is just a rhythm that isn’t yet resolved. Because the Public Key carries its “past” and “identity” within its current coordinates, it is structurally locked to the reference field. This effectively ends the era of “Mathematics as a Shield” and begins the era of “Structure as Governance.” And this has serious implications to the value , if any remains, of crypto.
When Breaking Elliptic Curve Cryptography (ECC) is a Piece of Cake Linearizing secp256k1 through Midpoint Symmetry (January 05, 2026). Available at SSRN


How is it that you found this concept